Thursday, June 19, 2008
A Kidnapped AdWords Account
This is the story of Russell, whose AdWords campaigns fell prey to a phishing scam.
Russell advertises one of his websites (WorldLabel.com) using AdWords, Google’s program that will launch advertisements on search results and third-party websites using AdSense. Russell is not a large-scale advertiser, so he only had a single campaign has six campaigns set up, he tells me.
Seemingly out of the blue, Russell one day noticed how a lot of odd, likely spammy campaigns had been set up in his account though. Take a look at the screenshot:
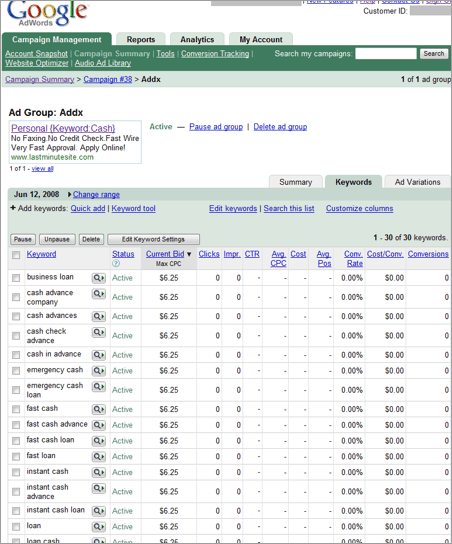
The keywords targeted for this campaign are all variations on “loans”, “fast cash” and so on. The maximum cost per click was set to $6.25.
Now apparently, Russell suggests that Google may have had some kind of “spam flag” raised, because these campaigns were immediately stopped. All Google would tell Russell, he says, “is they have several systems in place which Flags any ’unusual account activity’ which immediately stops all ads running until they have the time to check into it.” (Otherwise, Russell tells me Google wasn’t always that responsive throughout this incident.)
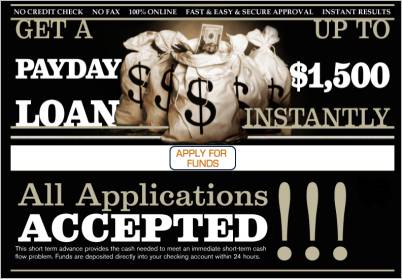
What’s LastMinuteSite.com, the site being advertised? Well, here’s a screenshot – the site claims to offer you a loan for $1,500 instantly with “all applications accepted” (it seems to be an affiliate program using SourceOnePayday.com). Note the site may or may not be the true origin site of the attack, as it may make sense for a malicious attacker to hide their tracks, camouflage style, by pointing to innocent sites as well:
Russell didn’t know what happened but with a little research we found out that prior to this AdWords kidnapping incident, he received an odd mail in his Hotmail account, apparently from the AdWords team. If you know about online security you will know what this means: it’s a phishing email, a seemingly legit official email asking you to e.g. log-in to your account to adjust some settings. Here’s a screenshot:
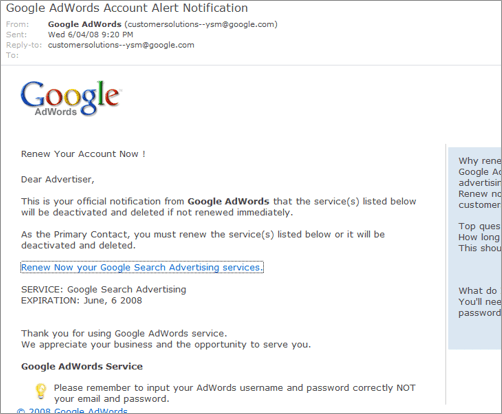
While the email may look official at first glance to those who don’t know about the concept of phishing – Russell didn’t – those who do know about it will have a symphony of alarm bells ringing by now. In this email, it is not important what the mail claims to be; it claims that it’s an “official notification from Google AdWords that the service(s) listed below will be deactivated” unless the person renews them “immediately.” The email also claims to be sent from the address customersolutions--ysm@google.com. But these things can be faked; what is more important is the URL that shows when you hover over the link in question that will take you to the login form. In this case, Russell tells me the URL reads:
yms-words.com/adwords/select/Login.htm
When visiting above URL – I logged out of my Google account first and disabled JavaScript – I can see it brings up a “Reported Web Forgery” alert thanks to my Firefox browser, and if I ignore that alert, it’s now a deserted, parked domain. But before, it was well possible that it displayed something that looked like an official Google AdWords log-in box. But when you enter your user account and password, those credentials will actually be submitted to the phishing attempt owner, who can then use it to log-in to someone else’s AdWords account to set up campaigns.
And indeed, Russell logged in to “his account” on that page, or so he figured, but actually that was the moment someone else likely fished for his password (or “phished”, in hack slang – the “ph” spelling was originally used in the context of phone system hacking, “phreaking”). Russell says after clicking through he went to his account “but could not find anything about renewing my Adwords.” Indeed, after the credentials are kidnapped, the phishing site can forward one to any other site – including the official AdWords site. It doesn’t matter at that point, and will make the incident look more innocent.
The best suggestion if you’re getting an email asking you to log-in somewhere is to either ignore it, or to not click any link in that email but instead open a new browser window and enter the URL (like “amazon.com”, “google.com” or whichever) manually. Hovering over the link in the email is also often a good first give-away, as the domain may not be the official one; still, there are some automatic forwarding schemes which may even make the domain look official, so it’s best not to click on such links at all. It’s too late for Russell, who by now changed his Google account password... though in this case he was apparently saved by Google’s AdWords abuse filter.
[Thanks Russell!]
>> More posts
Advertisement
This site unofficially covers Google™ and more with some rights reserved. Join our forum!
