Thursday, July 24, 2008
Google Account Phishing Attempt Using Orkut
By Tony Ruscoe
Earlier this week, I received a greetings card from someone called Shelia who was using “Orkut Greetings” (supposedly a service offered by Orkut, Google’s social network). Or at least that’s what the sender of this email wanted me to believe:
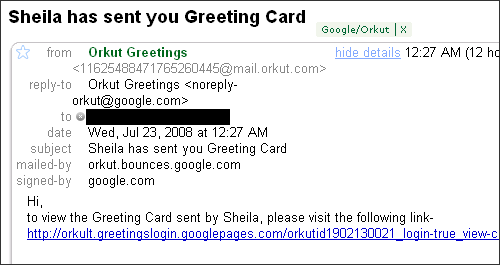
Those extra details are usually hidden by default, but I expanded them to verify that the email genuinely came from Google. It appears to have been sent from an Orkut email address and was even signed by the google.com domain. Seems genuine so far? Take a look at the domain in the link:
http://orkult.greetingslogin.googlepages.com
As you can see, the email isn’t sending me to Orkut at all. It’s actually sending me to a page hosted on Google Pages, a place where Google allows users to create and upload their own web pages. And here’s what the page looked like, which was asking me to sign in using my Google Account:
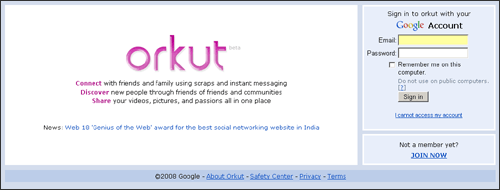
Everybody should already know not to enter their Google Account username and password on any website that isn’t being hosted on a google.com domain, so most people would hopefully spot this before handing their details over to the phisher. But what makes this email more convincing for the unsuspecting recipient is that the email was genuinely sent by Google. So how did the phisher do that?
If we take a look at the very bottom of the email – after 137 carriage returns, which are used to try and make sure you don’t see it – we can see this:
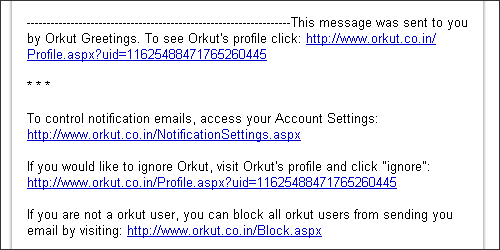
By creating an Orkut group – called Orkut Greetings – they were able to send messages from an Orkut email address which automatically gets signed by google.com since it’s being sent my Google’s systems and, therefore, make it appear to be genuine at first glance. By hosting their phishing doorway page on another Google property, they were able to make their sign in page appear to be almost genuine too.
After contacting Google shortly after receiving the email, I can confirm that the website on Google Pages was disabled some hours later due to violations of their Program Policies.
>> More posts
Advertisement
This site unofficially covers Google™ and more with some rights reserved. Join our forum!
